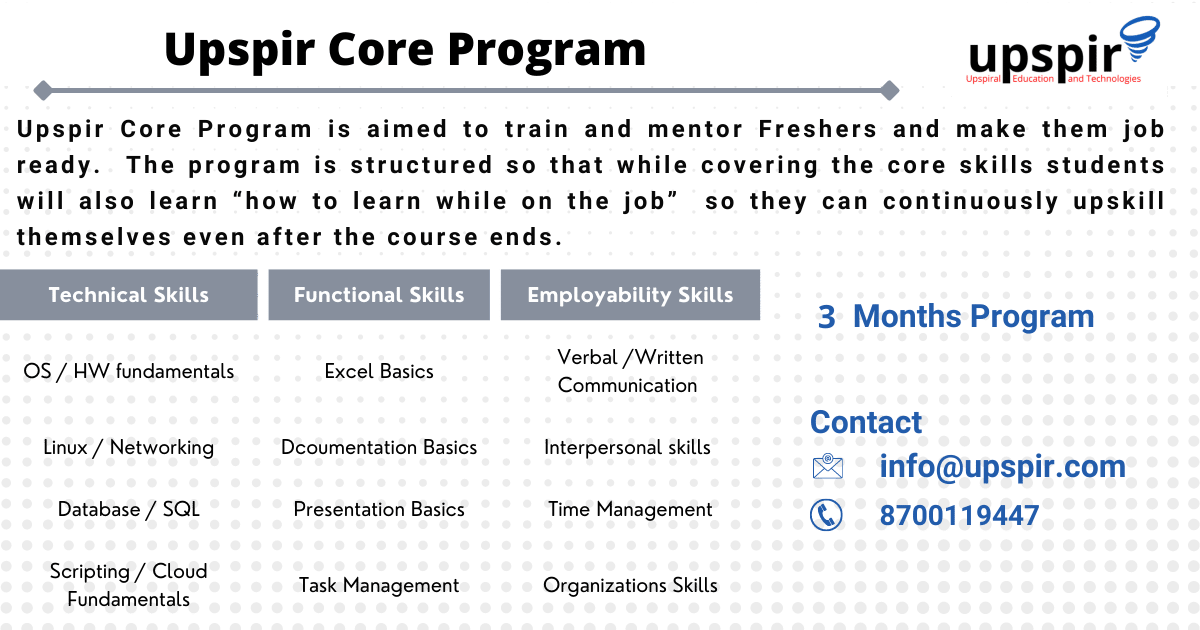
Today every computer is connected to some other computer through a network whether internally or externally to exchange some information. This network can be small as some computers connected in your home or office, or can be large or complicated as in large offices or the entire Internet.
Maintaining a system’s network is a task of the System/Network administrator.
Here is a list of 10 Networking commands that must be known to the network administrator/tech support engineer
- ifconfig
- ip
- ping
- traceroute
- netstat
- telnet
- dig
- netcat
- nmap
- Wireshark
1. ifconfig
ifconfig, will be one of the most used commands and for a long time it was the default command used to configure and troubleshoot network interface and issues on linux, ifconfig is a command-line interface tool for network interface configuration and is also used to initialize interfaces at system boot time.
It is also used to view the IP Address, Hardware / MAC address, as well as MTU (Maximum Transmission Unit) size of the currently active interfaces.
Running ifconfig without any arguments, lists all the interfaces which are currently in operation
ifconfig
To list all interfaces which are currently available, whether up or down, use the -a flag
[centos@midas ~]$ ifconfig -a
enp3s0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
inet 192.168.1.152 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::da72:6a96:b4cc:b4d6 prefixlen 64 scopeid 0x20<link>
ether 00:e0:4d:1e:b3:1c txqueuelen 1000 (Ethernet)
RX packets 1443 bytes 111527 (108.9 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 124 bytes 10010 (9.7 KiB)
TX errors 8 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1000 (Local Loopback)
RX packets 144 bytes 12836 (12.5 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 144 bytes 12836 (12.5 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
wlp0s20u6: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.29.22 netmask 255.255.255.0 broadcast 192.168.29.255
inet6 fe80::6ebc:877a:f6c0:885c prefixlen 64 scopeid 0x20<link>
inet6 2405:201:4019:91a2:d7c7:e3b2:ae40:468a prefixlen 64 scopeid 0x0<global>
ether 3c:33:00:60:48:f8 txqueuelen 1000 (Ethernet)
RX packets 551536 bytes 105040791 (100.1 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 51404 bytes 5621067 (5.3 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
Viewing the configuration of a specific interface
[centos@midas ~]$ ifconfig enp3s0
enp3s0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
inet 192.168.1.152 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::da72:6a96:b4cc:b4d6 prefixlen 64 scopeid 0x20<link>
ether 00:e0:4d:1e:b3:1c txqueuelen 1000 (Ethernet)
RX packets 1443 bytes 111527 (108.9 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 124 bytes 10010 (9.7 KiB)
TX errors 8 dropped 0 overruns 0 carrier 0 collisions 0
Configuring an interface
[root@midas ~]# ifconfig enp3s0 192.168.1.122 netmask 255.255.255.0 broadcast 192.168.1.255
[root@midas ~]# ifconfig enp3s0
enp3s0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
inet 192.168.1.122 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::da72:6a96:b4cc:b4d6 prefixlen 64 scopeid 0x20<link>
ether 00:e0:4d:1e:b3:1c txqueuelen 1000 (Ethernet)
RX packets 1443 bytes 111527 (108.9 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 124 bytes 10010 (9.7 KiB)
TX errors 8 dropped 0 overruns 0 carrier 0 collisions 0
2. IP
The IP command is the new default networking command for linux and has replaced ifconfig, it is a part of iproute2util package. IP command takes different flags and syntax than if config command. The ip command is more versatile and technically more efficient than ifconfig because it uses Netlink sockets, though the syntax can be more complex than ifconfig
To list all the all the interfaces we can use “”ip addr show”” or “”ip a”” for short
[root@midas ~]# ip addr show
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: enp3s0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc fq_codel state DOWN group default qlen 1000
link/ether 00:e0:4d:1e:b3:1c brd ff:ff:ff:ff:ff:ff
inet 192.168.1.122/24 brd 192.168.1.255 scope global noprefixroute enp3s0
valid_lft forever preferred_lft forever
inet6 fe80::da72:6a96:b4cc:b4d6/64 scope link noprefixroute
valid_lft forever preferred_lft forever
3: wlp0s20u6: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 3c:33:00:60:48:f8 brd ff:ff:ff:ff:ff:ff
inet 192.168.29.22/24 brd 192.168.29.255 scope global dynamic noprefixroute wlp0s20u6
valid_lft 15969sec preferred_lft 15969sec
inet6 2405:201:4019:91a2:d7c7:e3b2:ae40:468a/64 scope global dynamic noprefixroute
valid_lft 3596sec preferred_lft 3596sec
inet6 fe80::6ebc:877a:f6c0:885c/64 scope link noprefixroute
valid_lft forever preferred_lft forever
Add IP address
[root@midas ~]# ip a add 192.168.1.152/24 dev enp3s0
[root@midas ~]# ip a show enp3s0
2: enp3s0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc fq_codel state DOWN group default qlen 1000
link/ether 00:e0:4d:1e:b3:1c brd ff:ff:ff:ff:ff:ff
inet 192.168.1.122/24 brd 192.168.1.255 scope global noprefixroute enp3s0
valid_lft forever preferred_lft forever
inet 192.168.1.152/24 brd 192.168.1.255 scope global secondary noprefixroute enp3s0
valid_lft forever preferred_lft forever
inet6 fe80::da72:6a96:b4cc:b4d6/64 scope link noprefixroute
valid_lft forever preferred_lft forever
Enable or disable a network
ip commands uses the set sub command for this operation
ip link set enp3s0 up
ip link set enp3s0 down
3. Ping
Ping is a simple, widely used, cross-platform networking utility for testing if a host is reachable on an Internet Protocol (IP) network. It works by sending a series of Internet Control Message Protocol (ICMP)
ping is a very common and relatively simple command, but it also provides there are some great options and techniques that make the tool even better, to troubleshoot connectivity issues
[root@midas ~]# ping 192.168.29.1
PING 192.168.29.1 (192.168.29.1) 56(84) bytes of data.
64 bytes from 192.168.29.1: icmp_seq=1 ttl=64 time=1.59 ms
64 bytes from 192.168.29.1: icmp_seq=2 ttl=64 time=2.00 ms
64 bytes from 192.168.29.1: icmp_seq=3 ttl=64 time=1.30 ms
64 bytes from 192.168.29.1: icmp_seq=4 ttl=64 time=1.49 ms
^C
--- 192.168.29.1 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3004ms
rtt min/avg/max/mdev = 1.303/1.592/1.995/0.253 ms
ping -a <host>, adds audible cue, giving a system sound whenever the pings are successful
ping -c <host>, lets you adjust the number of pings
ping <hostname> also lets you display the ip address of the hostname
Output from ping
- ping output provides some useful insights into the quality of the network, the most important metrics are packet loss, time,
- whether the target host is reachable (active) or not,
- to measure the amount of time it takes for packets to get to the target host and back to your computer
- the packet loss, expressed as a percentage.
- timeout message indicates that your machine believes it sent successful ping queries to the destination but it did not receive the replies in the specified time
- TTL means “”time to live””. It is a value on an ICMP packet and this value is decreased every time a router touches the packet. If the TTL ever reaches zero, the packet is discarded. It is a measure of the number of hops the packet took to reach the destination, if your initial value was 64 and now you see a value of 28 there are 36 hops between the originated and final destination
- Time metric can also be used to assess the quality of the network and it provides insights into latency and jitter in the network, a high response time signifies high latency, where as a fluctuating time value in response signifies jitter.
4. Traceroute
Traceroute is a command-line utility for tracing the full path from your local system to another network system. It prints a number of hops (router IPs) in that path you travel to reach the end server. It is an easy-to-use network troubleshooting utility after the ping command
5. Netstat (network statistics)
netstat (network statistics) is the command-line tool for monitoring network connections both incoming and outgoing as well as viewing routing tables, interface statistics, etc. It can be used for troubleshooting and for configuration.
Listing all ports
Note : we have used more to control the output, it is not necessary
[root@midas ~]# netstat -a | more
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State
tcp 0 0 localhost:ipp 0.0.0.0:* LISTEN
tcp 0 0 0.0.0.0:ssh 0.0.0.0:* LISTEN
tcp 0 96 midas.upspiroffice.:ssh 192.168.29.147:53980 ESTABLISHED
tcp6 0 0 [::]:ssh [::]:* LISTEN
tcp6 0 0 localhost:ipp [::]:* LISTEN
udp 0 0 0.0.0.0:mdns 0.0.0.0:*
udp 0 0 0.0.0.0:47053 0.0.0.0:*
udp 0 0 midas.upspiroffi:bootpc reliance.relianc:bootps ESTABLISHED
udp 0 0 localhost:323 0.0.0.0:*
udp6 0 0 [::]:mdns [::]:*
List only TCP port connections
For listing only TCP (Transmission Control Protocol) port connections using netstat -at.
[root@midas ~]# netstat -at
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State
tcp 0 0 localhost:ipp 0.0.0.0:* LISTEN
tcp 0 0 0.0.0.0:ssh 0.0.0.0:* LISTEN
tcp 0 288 midas.upspiroffice.:ssh 192.168.29.147:53980 ESTABLISHED
tcp6 0 0 [::]:ssh [::]:* LISTEN
tcp6 0 0 localhost:ipp [::]:* LISTEN
[root@midas ~]#
Listing all active listening ports netstat -l
Listing all active listening UDP ports by using option netstat -lu
Showing network interface packet transactions including both transferring and receiving packets with MTU size
[root@midas ~]# netstat -i
Kernel Interface table
Iface MTU RX-OK RX-ERR RX-DRP RX-OVR TX-OK TX-ERR TX-DRP TX-OVR Flg
enp3s0 1500 133 0 0 0 38 5 0 0 BMRU
lo 65536 44 0 0 0 44 0 0 0 LRU
wlp0s20u6 1500 844 0 0 0 198 0 0 0 BMRU
6. Telnet
Telnet command is used to establish the connections between different machines. This command allows us to manage the remote devices using the CLI (command-line interface)
Open a connection with a remote host
[root@localhost centos]# telnet 192.168.1.22 80
Trying 192.168.29.22...
Connected to 192.168.29.22.
Escape character is '^]'.
If no port is specified, it uses TCP port 23 which is assigned to the telnet protocol
7. Nslookup
tool for testing and troubleshooting DNS servers (Domain Name Server). It is used to query specific DNS resource records (RR) as well
8. Dig (Domain Information Groper)
just like nslookup command, this command is used for querying and getting information of DNS (Domain Name System).
Dig stands for (Domain Information Groper) is a network administration command-line tool for querying Domain Name System (DNS) name servers.
[root@localhost centos]# dig yahoo.com
; <<>> DiG 9.16.23-RH <<>> yahoo.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 26615
;; flags: qr rd ra ad; QUERY: 1, ANSWER: 6, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;yahoo.com. IN A
;; ANSWER SECTION:
yahoo.com. 561 IN A 74.6.231.21
yahoo.com. 561 IN A 74.6.231.20
yahoo.com. 561 IN A 74.6.143.25
yahoo.com. 561 IN A 98.137.11.163
yahoo.com. 561 IN A 98.137.11.164
yahoo.com. 561 IN A 74.6.143.26
;; Query time: 2 msec
;; SERVER: 192.168.29.1#53(192.168.29.1)
;; WHEN: Thu Sep 29 15:27:37 IST 2022
;; MSG SIZE rcvd: 123
Dig command reads the /etc/resolv.conf file and querying the DNS servers listed there
To query domain “A” record with +short
[root@localhost centos]# dig yahoo.com +short
98.137.11.164
74.6.143.26
74.6.231.21
74.6.231.20
74.6.143.25
98.137.11.163
9. Netcat
Netcat (or nc in short) is a simple yet powerful networking command-line tool used for performing any operation in Linux related to TCP, UDP, or UNIX-domain sockets.
Netcat can be used for port redirection, as a port listener (for incoming connections); it can also be used to open remote connections and so many other things. Besides, you can use it as a backdoor to gain access to a target server.
Here is an example, the -z option sets nc to simply scan for listening daemons, without actually sending any data to them. The -v option enables verbose mode and -w specifies a timeout for connection that can not be established.
10. Nmap
Network Mapper is an open-source and a very versatile tool for Linux system/network administrators. Nmap is used for exploring networks, performing security scans, network audit,s and finding open ports on the remote machine
Nmap allows you to scan your network, to discover not only what is connected to it but also a host of other information like what devices are listening on which ports, it comes with a large number of scanning techniques and filters.
Scan a System with Hostname and IP Address
to find out all open ports, services and MAC addresses on the system.
nmap hostname
nmap ipaddress
[root@midas centos]# nmap 192.168.29.44
Starting Nmap 7.91 ( https://nmap.org ) at 2022-09-29 15:42 IST
Nmap scan report for 192.168.29.44
Host is up (0.021s latency).
Not shown: 997 filtered ports
PORT STATE SERVICE
22/tcp open ssh
2049/tcp open nfs
MAC Address: 80:86:F2:47:E4:C4 (Intel Corporate)
Nmap done: 1 IP address (1 host up) scanned in 10.53 seconds
….
…..
Author
Pravin Tewari
Senior Manager, Application and Cloud Support
Pravin is a visionary professional with over 11 years of experience in Technical Support, Cloud Infrastructure Management, and Customer Experience. He has hands-on experience in working across the lifecycle of project delivery and deployment, solution consulting, and support. He has deep experience in managing cloud deployments and implementing DevOps tools for automation to provide better uptime. Pravin has successfully led large product & cloud support teams, and coached & mentored a high-performing team that delivers high-quality service to customers.